Cloud Security What is cloud security?
Cloud security is a subset of cyber security that involves a multi-pronged approach to protecting all assets that are placed on a cloud, including virtualized IP, data, applications, services, and cloud infrastructure.
Table of Contents
Why is cloud security important?
According to recent research, 97 percent of organizations across the globe use some form of cloud service. Of that total, 25 percent have had data stolen, and 20 percent have had their cloud infrastructure attacked.
Being on a cloud platform introduces new risks that enterprises must prioritize within their cyber security programs. A robust cloud security program establishes the policies, technologies, applications, and controls used to protect an enterprise from threats.

The impact of security in hybrid cloud
Security is an ongoing process, not a destination. Hybrid cloud offers flexibility with security for on-premises data and leveraging cloud provider expertise for cloud-based data. This frees up IT to focus on business needs. Additionally, hybrid cloud allows for compliance, data transfer security (VPNs), and redundancy, all mitigating various risks while introducing some manageable overhead.

Types of cloud security
Modern enterprises use cloud computing for scalability, flexibility, and affordability. As enterprises go to the cloud, data and infrastructure security become crucial. Cloud Security has multiple levels, each addressing specific issues. Here's about network, data, application, identity, and access management security.
- Network security:
- Relevance: The first line of defence in cloud computing is network security. It secures cloud infrastructure communication channels from unwanted access, data breaches, and cyberattacks.
- Approach: Firewalls, intrusion detection and prevention systems (IDPS), VPNs, and SSL encryption protect data during transmission. Identification and mitigation of possible security issues are strengthened by routine network traffic audits and monitoring.
- Security Service Edge:
- Relevance: Cloud adoption can increase exposure to dangerous cyber threats. Organizations need to deliver secure access for all users, from any device, from anywhere, to cloud applications.
- Approach: Key security technologies such as Secure Web Gateway, Cloud Access Security Broker, Zero Trust Network Access, and Digital Experience Monitoring, as well as capabilities such as mesh connectivity for resilience of cloud-delivered security services, enable organizations to reduce risk without sacrificing performance.
- Data security:
- Relevance: Data is an organization's lifeblood; therefore, protecting it is crucial. Data security in the cloud protects sensitive data from unwanted access, loss, and corruption.
- Approach: Data encryption at rest and in transit increases security. A strong cloud data security plan includes access limits, DLP technologies, and frequent backups. Compliance with industry standards and laws increases data integrity and confidentiality.
- Application security:
- Relevance: Cloud services are dependent upon applications. They must be secured to prevent attackers from exploiting vulnerabilities.
- Approach: To fix vulnerabilities, apps must be updated and patched regularly. WAFs, code reviews, and penetration testing find and resolve security vulnerabilities. Containerization and microservices design isolated components, improving application security.
- Access and identity management:
- Relevance: Managing user identities and restricting resource access are key to cloud security. Unauthorized access can endanger infrastructure and breach data.
- Approach: Multi-factor authentication (MFA) restricts cloud resource access to authorized users. RBAC assigns rights based on work responsibilities, reducing unwanted access. Regularly assessing and changing user privileges improves security.
A complete cloud security plan addresses network, data, application, identity, and access management. Organizations must use technology, regulations, and continual monitoring to protect digital assets in the ever-changing cloud environment. Maintaining a robust and secure cloud infrastructure requires remaining educated and modifying security measures as technology evolves.

How does cloud security work?
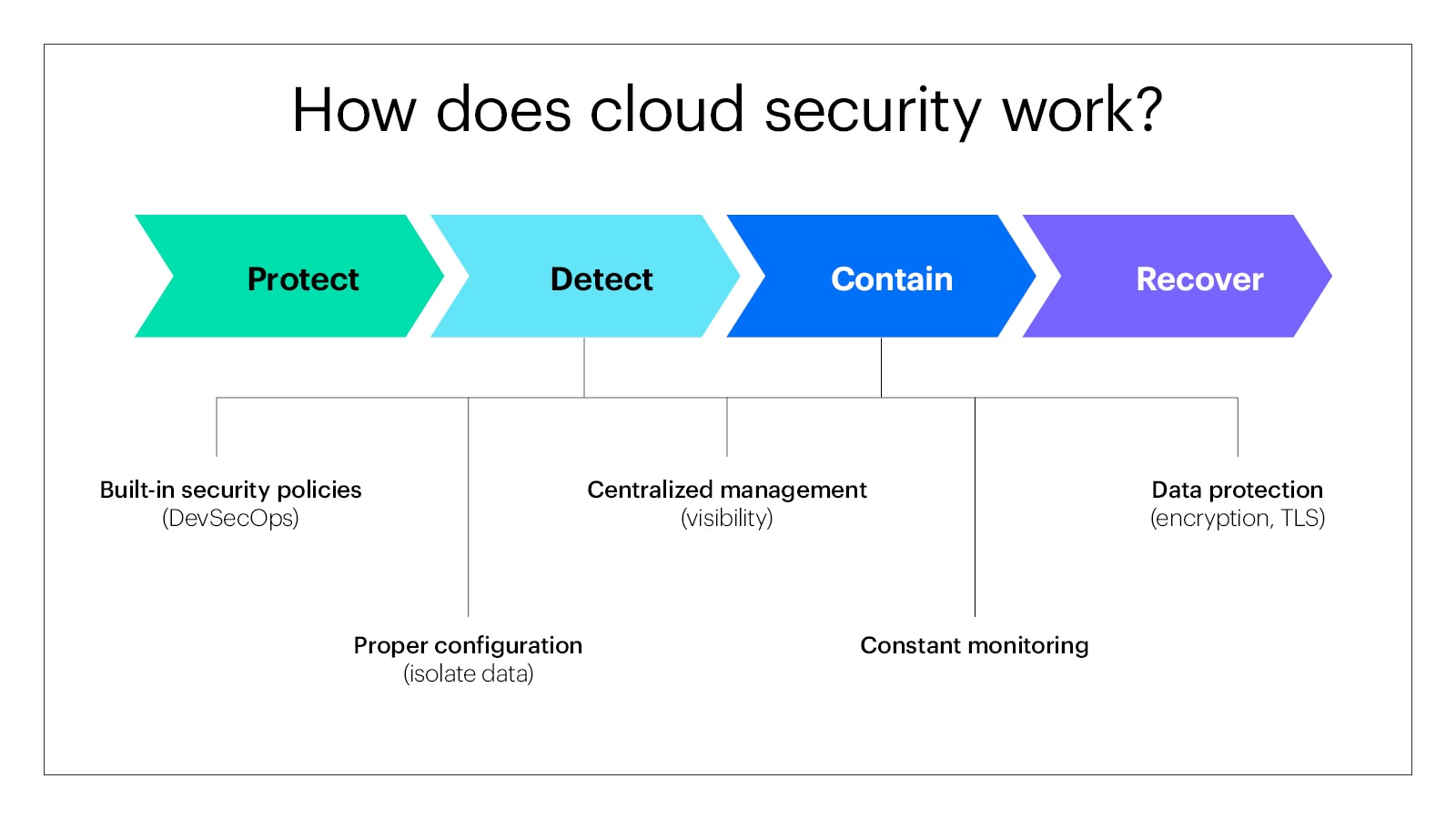
A cloud security program monitors all activity in the cloud and has established plans in place to react quickly in the event of a breach. In general, cloud security has four main objectives: protect, detect, contain, and recover.
To accomplish these four goals, enterprises deploy a mix of policies, tools, and controls that are then always in effect.
- Policies: Enterprises should build security into the development process of any product or service. That means that rather than relying on a separate security verification team, a policy should mandate that DevOps and DevSecOps be included within the business unit creating the new offering. A policy that requires departments and personnel to participate in asset identification, classification, and accountability also helps build awareness and protection.
- Proper configuration: IT departments need to configure cloud assets to separate data from operations and automatically identify and permit access to only the people and systems that need it to do their jobs.
- Centralized management: Many organizations implement different cloud solutions, with different providers who offer their own management tools. Unifying cloud security across all services and providers gives IT visibility into every access point from one place, making it easier to monitor and detect threats.
- Constant monitoring: Using tools that are readily available, IT can see what cloud computing platforms and services their users are accessing and what activities might put the organization at risk. In addition, such tools can ensure that all security and compliance requirements are met 24/7. Regular audits of apps and devices in use and assessments of potential risks should also always be on.
- Data protection: Enterprises use a variety of tactics to prevent data loss and/or spillage. These include VPN, encryption, masking (encrypting identifying info), and Transport Layer Security (TLS) to prevent eavesdropping and tampering with messages.
- Maintenance: Maintaining redundancy and full data backups stored somewhere else is essential, and many service providers bundle these into their subscriptions. Moreover, keeping up with updates and security patch software is usually handled by the service provider, but internal IT is responsible for patching their own services.
What are the benefits of cloud security?
The ability to mitigate threats benefits an enterprise, keeping operations running full-bore despite the risks of using cloud services. The main advantages of cloud security boil down to what it prevents: unauthorized users and malicious activity. The following are a mix of advantages to implementing a cloud security program.
- Preventing DDoS attacks: With constant monitoring and analysis and mitigation tools, cloud security programs are prepared to stamp out the growing threat of these sophisticated attacks.
- Protecting data: By separating data from users and applications, sensitive data is pooled in a secure place where access is automatically controlled.
- Greater visibility: With one integrated cloud security program, IT has a single point from which they can monitor all activity, rather than having to keep an eye on multiple clouds.
- Higher availability: Due to the redundancies built into cloud security, resources and applications are always on and ready for access.
- Regulatory compliance: By automatically encrypting data during transmission and controlling access to it when it’s stored, organizations meet DOD and federal regulations.
- Business continuity: The redundancies built into cloud security not only secure data and resources from bad actors, they also serve to ensure that business operations can continue despite weather and power disruptions.


What challenges does cloud security need to overcome?
As the volume and pace of cloud deployments increases, so too do the risks to the overall resources placed on the cloud. Companies often use multiple clouds at the same time, with different clouds for different functions, further multiplying those risks. The following are some of the challenges to cloud-based security.
- Awareness: Placing so many resources and activities off premises and on the cloud means that IT has poor visibility into every point of access. These avenues are much more easily controlled when everything resides on premises.
- DDoS Attacks: Record-breaking numbers of Distributed Denial of Service (DDOS) attacks make keeping up with the pace a real strain on all players involved on the cloud—including providers and subscribers. The speed and agility needed continues to climb and the burden must be shared across organizations and providers.
- Integration: To reduce the risk of sensitive information flows to and through cloud services, integrating on-site data loss prevention with cloud providers is a must. IT should run manual or automated data classification even before uploading the data to the cloud and keep user authorization controls in house.
- Insiders: Sometimes the threat comes from internal users, whether intentional or accidental. IT should have a three-pronged approach to mitigating this risk:
- Restricting sensitive data to only managed devices
- Using behavioral analytics to monitor activity
- Training users frequently

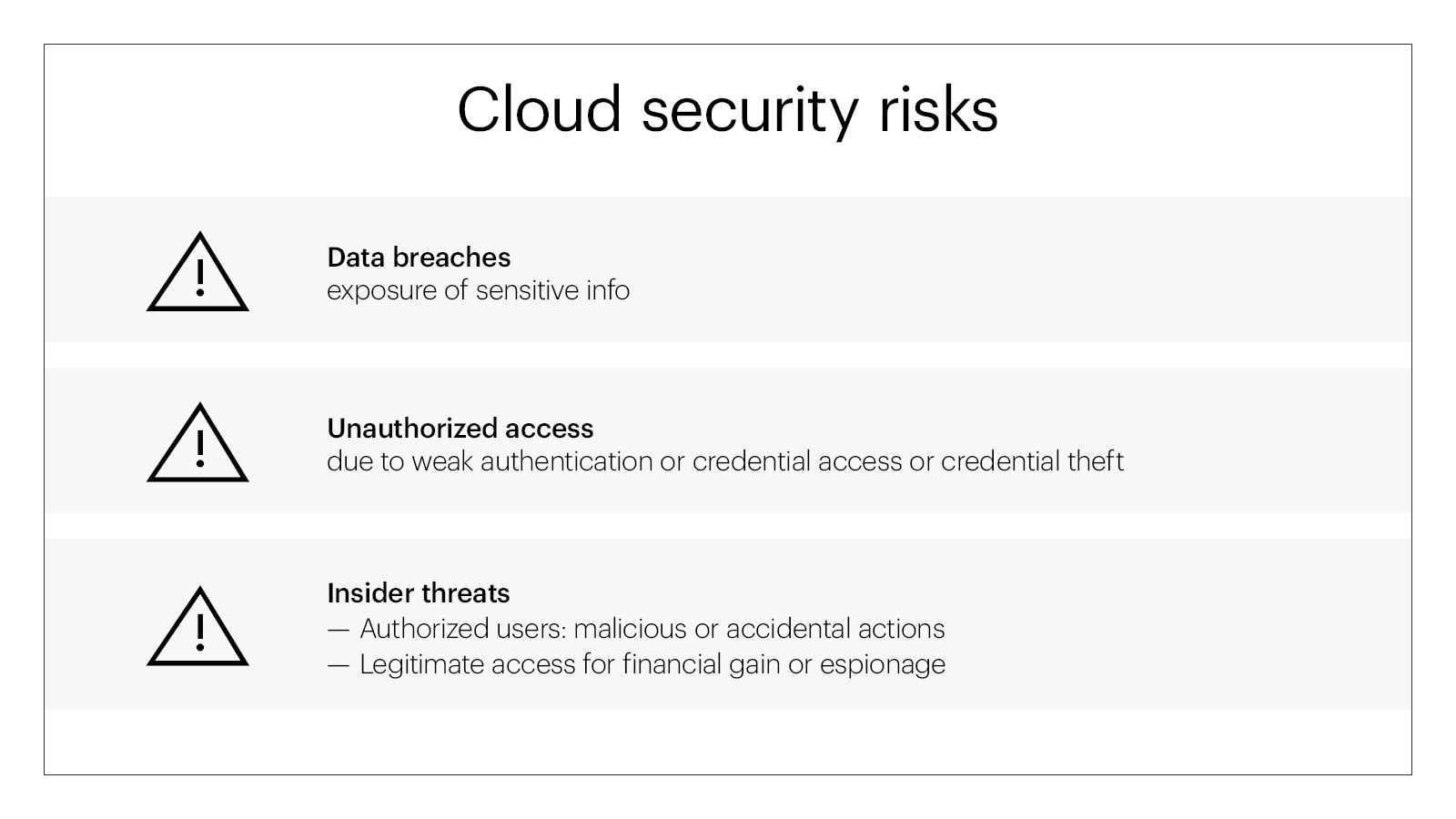
Cloud security risks
Cloud computing has many benefits, but enterprises must address security threats to protect their digital assets. Here are significant cloud security risks:
- Data breaches:
- Risks: Cloud computing risks involve sensitive data exposure, unauthorized access, theft, and disclosure due to breaches. Attackers may exploit cloud service vulnerabilities or poorly set up storage.
- Types of data breaches: Data breaches can result from internal events, which are frequently brought on by incorrectly configured settings or insufficient access restrictions, and external assaults, in which hackers compromise cloud infrastructure.
- Unauthorized access:
- Risks: Unauthorized access is the result of people or organizations accessing cloud resources without the required authority. This can cause data alteration, theft, or service outages.
- Types of unauthorized access: Common techniques for unauthorized access include credential theft, weak authentication procedures, and taking advantage of security holes in cloud platforms. Insufficient access restrictions and user permission mishandling can further increase this danger.
- Insider threats:
- Risks: Insider threats are harmful acts carried out by persons with legitimate access to the cloud environment. This might include workers, contractors, or partners that abuse their powers or inflict harm.
- Types of Insider Threats: In addition to unintentional acts like clicking on phishing links, malicious insiders can deliberately divulge confidential information. Insiders can use their power for financial gain, revenge, or espionage, making identifying and avoiding them difficult.
Strong authentication, encryption, access controls, and continual monitoring are needed to mitigate these threats. To address changing cloud security issues, organizations must stay watchful, upgrade security, and educate users.
Cloud security best practices
Enterprises must implement strong cloud computing security safeguards to safeguard critical data and processes. Best practices for cloud security are:
- Use strong passwords:
Importance: Strong passwords are the first line of security against unauthorized access. They protect cloud platform user accounts from illegal access.
Tips for creating strong passwords:
- Use upper and lowercase letters, numbers, and symbols to create a strong password.
- Keep information that can be guessed readily away, such as birthdays or common phrases.
- Make sure each account has a unique password.
- Update passwords often and avoid guessable sequences.
- Implement multi-factor authentication (MFA):
Importance: Multi-factor authentication boosts online security by requiring users to provide multiple forms of identification. This dramatically prevents unwanted access, even with compromised credentials.
Types of MFA:
- Email codes or text messages: A one-time code delivered to an email address or registered cellphone number.
- Biometric Authentication: Scannable fingerprints, faces, or retinas.
- Hardware tokens: Physical devices generating time-sensitive codes.
- App-Based Authentication: Using mobile apps such as Authy or Google Authenticator.
- Regularly back up data:
Importance: Data loss can result from cyberattacks, device problems, or accidental deletions. Regular backups allow firms to rapidly recover and restore operations if data is lost.
Backup methods:
- Automatic frequent backups: Schedule frequent backups to reduce data loss.
- Offsite backups: Avoid single-point failure by storing backups elsewhere or in the cloud.
- Versioning: Save files several times to avoid corruption.
Following these best practices strengthens cloud computing security. Organizations must prioritize user authentication, data security, and recovery to design a robust cloud architecture that can endure the changing digital world. A safe cloud system requires constant monitoring and adaptability to new security threats.

Zero trust in cloud security
Zero trust challenges the perimeter-based strategy by presuming attacks could originate from within and outside an organization's network. This is especially important in cloud security, as data and services are distributed across several environments.
Zero trust requires authentication from everyone seeking resource access, regardless of location or network connectivity. Cloud computing is dynamic. Therefore, strong authentication, access restrictions, and continual monitoring are needed.
Implementing zero trust in cloud security involves several key principles:
- Focus on user identities and robust authentication to provide access.
- Grant the minimum access needed for people to complete their jobs to reduce the effect of compromised credentials.
- Monitoring user activity and network traffic in real time can reveal anomalies and security issues.
- To prevent breaches and restrict lateral movement inside the infrastructure, micro-segment the network into smaller, more isolated sections.
Zero trust cloud security recognizes that trust should never be assumed and that security measures should be continually implemented, updated, and validated to match the developing digital ecosystem threat scenario. This proactive method strengthens cloud infrastructures against external and internal threats, addressing ever-changing cybersecurity risks.
How does HPE help customers with cloud security?
Hewlett Packard Enterprise (HPE) offers a range of solutions and services to assist customers in enhancing their cloud security posture. Here's an overview of how HPE addresses cloud security challenges through various offerings:
- GreenLake suite of cloud and as-a-service solutions provides a cloud experience wherever applications and data live—edge, data center, colocation, and public cloud. Zero trust-enabled architecture from edge to cloud helps GreenLake address gaps and simplify security breaches. It protects the digital supply chain and ensures security and compliance with a risk-based and compliance-driven cyber resilience and data protection strategy.
- HPE Managed Security helps companies achieve security standards by giving visibility and control to safeguard corporate processes with comprehensive tools that cut costs and free up manpower. HPE Managed Security provides administration, visibility, and control tools on security-ready infrastructure to help businesses address security comprehensively. With integrated security architecture and ongoing monitoring, it helps businesses implement a Zero Trust framework and detect and fix security weaknesses.
- Providing compliance monitoring, proactive remediation recommendations, and access to a reliable compliance expert, HPE Managed IT Compliance is a managed service that assists clients in locating and fixing security flaws and safeguarding their data and applications. HPE Managed IT Compliance uses standards-based procedures and best-in-class technologies to help clients keep ahead of growing compliance duties and minimize audit preparation time, cost, and complexity. Customer compliance with GDPR and CCPA is also handled by HPE Managed IT Compliance.
- HPE Data Protection protects clients' data from ransomware attacks and other threats with continuous data protection that provides always-on replication instead of snapshots. HPE Data Protection's built-in encryption ensures backup data security regardless of location.
- HPE Zero Trust Security is a solution designed to assist clients in implementing a Zero Trust framework in their edge-to-cloud settings. HPE Zero Trust Security provides granular visibility and control to secure data, devices, people, and applications from assaults. Customers can also reduce the attack surface, identify and respond to threats, and automate security operations using this solution.
- HPE Aruba Networking SSE delivers security connectivity using more than 500 edge locations to elegantly connect users and devices to the cloud and other resources needed for work. The platform artfully integrates Zero Trust Network Access (ZTNA), Secure Web Gateway (SWG), Cloud Access Security Broker (CASB), and Digital Experience Monitoring (DEM) into one, cloud-delivered platform that feels weightless, and is controlled by a single pane of glass.